Home, sweet, smart home. There is no smart home without smart home devices, but what about smart setups? From historical introductions to topics like smart lighting and smart remotes to thorough product overviews and setups for Logitech Harmony, Philips Hue, Nanoleaf Aurora, Nanoleaf Remote, and Dyson Pure (Hot and) Cool. From long-term reviews like for the Netatmo Weather Station and the Venta Airwashers to general concepts around smart devices.
Healthy Humidity with Venta Airwashers and Alexa, Siri and Google
We are mainly composed of water. The air we exhale is completely saturated with water. But, do you know the humidity of the 2,641 gallons (10,000 liters) of indoor air that you inhale, per day? It starts with a dry…
Breathe! Dyson Pure Cool with Siri, Alexa and Google
We spend about 90% of our time indoors. The last couple of months maybe even more and primarily at home. And while we’re at home, we breathe around 10,000 liters (2,641 gallons) of air, per day. Breathing is the only…
Philips Hue – The Smart Setup for Your Smart Lights
In this post, we will shed some light on the basic principles of smart lighting and the Philips Hue product family and generations. We will look into efficiently setting up – just a couple and also many – lights with the Philips Hue app and prepare a setup which we can easily integrate with our voice assistants: Siri, Alexa, and Google.
Netatmo Weather Station, Rain and Wind Gauge, and Alexa and Siri
This post is a long-term review. We’ll have a look how the Netatmo Weather Station, an additional Indoor module, the Rain Gauge, and the Wind Gauge performed over many years. And, how Alexa and Siri came into the picture.
Nanoleaf Remote Setup – The Shape of the Universe?
Don’t get me wrong, this post is about how to set up your Nanoleaf Remote! But the very first aspect which will catch your eye, way before you realize that this is a glowing remote control, is its shape. It’s…
Nanoleaf Aurora and the Rhythm Module: Visualize Your Music
It’s been a while since we have looked into the Nanoleaf Rhythm module for our Nanoleaf Aurora. The Nanoleaf app has meanwhile received a major update and the Rhythm section has a bunch of new visualizations for our music. Time…
Nanoleaf Aurora How To – Setup and Configuration to the Muks!
It’s been quite a while since we’ve looked into the setup and configuration of our Nanoleaf Aurora. Meanwhile, Nanoloeaf renamed the Aurora into “Light Panels”, redesigned the Nanoleaf app, added new features and we’ve extended our setup to the max…
Logitech Harmony – a Hub and it’s Elite, Ultimate, Companion
How many remote controls do you (have to) use? How many times are you searching for one of them, only to find you need the other one? Switching input channels and turning devices on, on multiple remotes, every single time….
Introduction to Smart Entertainment: A Brief History of Remotes
It is a rainy September afternoon in New York. We are at the first Electrical Exhibition held at Madison Square Garden. A tall, skinny man is standing next to a big pool, surrounded by an excited crowd. In the pool…
Introduction to Smart Lighting: A Very Brief History of Light
Just as light is a vital component of life, smart lighting is a cornerstone of our smart home. In this introduction post (thank you for the feedback, that we need such posts!), we will shed some light on the history…
Sleeping Better with Smart Lighting: Smarter “Go to Bed” and “Wake Up”
We spend 36% of our lives asleep, and while the average sleep period has decreased over the last 60 years, neuroscience is discovering more and more how important sleep is for our well-being. Can smart lighting help us to sleep…
The Many Ways of Controlling Smart Lighting
We have many options to control our smart lights. Some might appear traditional, like a simple light switch, but the possibilities we have nowadays to switch to our preferred lighting scenes, go way beyond only turning lights on and off….
Natural Smart Lighting: Feeling Better With Smart Light
We have already looked into the impact of light on our sleep in the “Sleeping Better with Smart Lighting” post. But what about the rest of the day? Can smart lighting help us to “feel better”, maybe by resembling natural…
Control Smart Lighting with Presence, Geo-fencing and Motion Sensors
We can control smart lighting in different ways, through our presence, or even during our recreational absence. Motion sensor activated lighting is definitely not a novelty. Samuel Bagno invented the first motion sensor already back in the early 1950s, but…
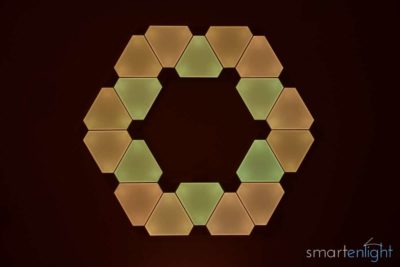
Nanoleaf Aurora – Smart Lighting, Living Paint or Smart Art?
Please note, we have upgraded our Nanoleaf Aurora setup and updated this post here: Nanoleaf Aurora How To: Setup and Configuration to the Muks! Nanoleaf Aurora provides a personal smart lighting experience which is indeed unlike anything I have seen before….